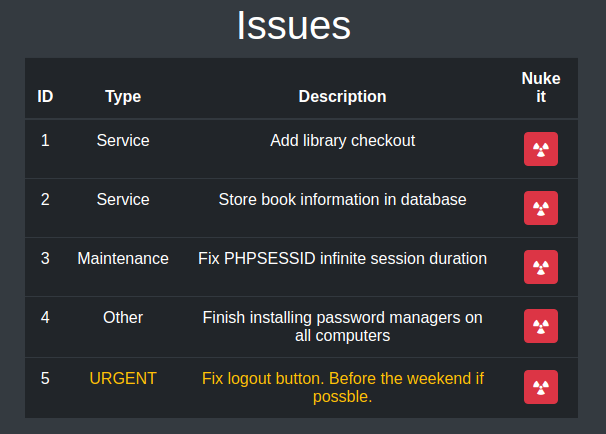
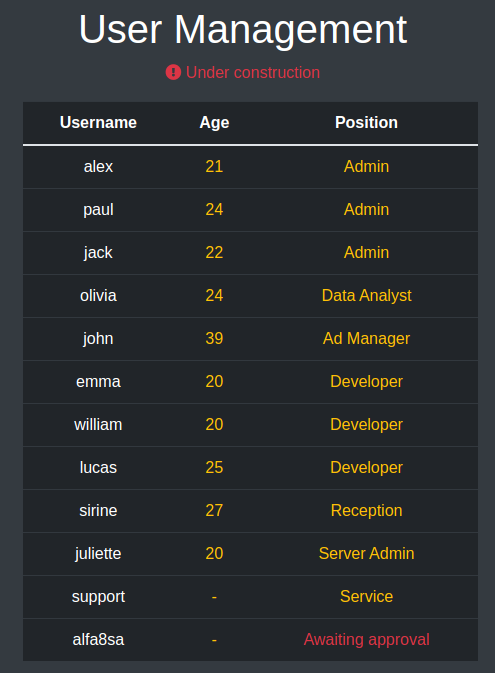
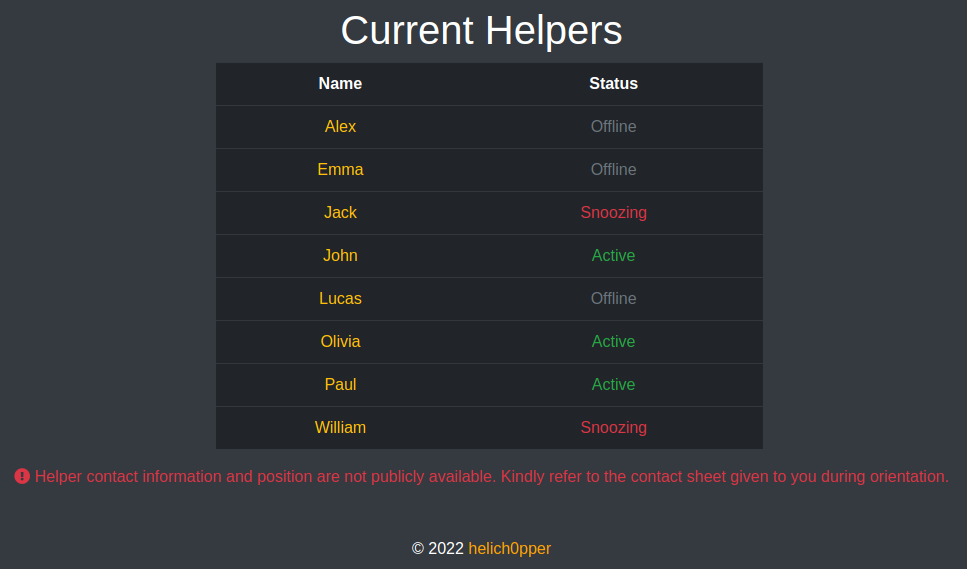
| Task |
Status |
Reason |
| Configure firewall for port 22 and 445 |
Not started |
Unauthorized access might be possible |
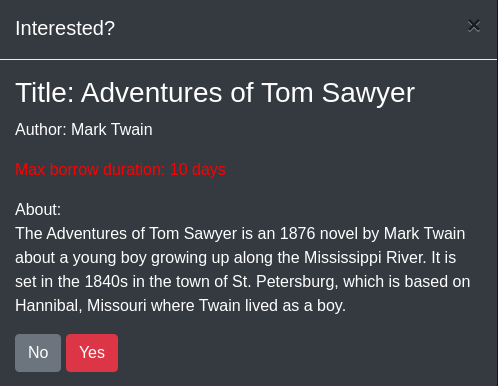
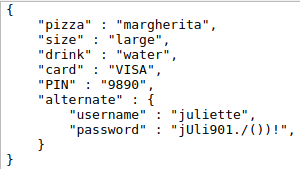
| Migrate passwords from the Microsoft Store Sticky Notes application to our new password manager |
In progress |
It stores passwords in plain text |
| Add new features to password manager |
Not started |
To get promoted, hopefully lol |
```
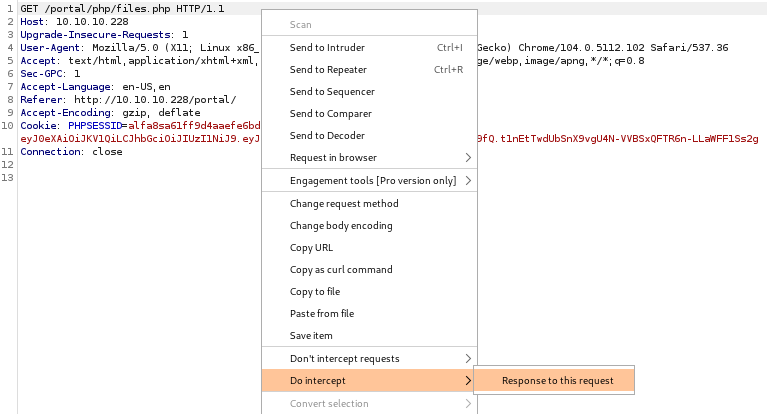
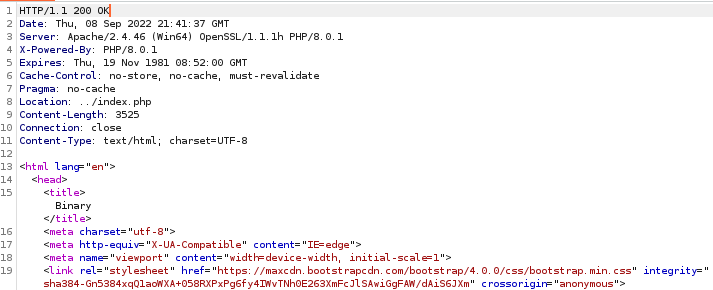
I look for the path where the Sticky Notes program is stored, and I found the `C:\Users\username\AppData\Roaming\Microsoft\Sticky Notes` path. But, in the machine, the *Sticky Notes* directory doesn't exist.
> dir \Users\juliette\AppData\Roaming\Microsoft
```
Volume in drive C has no label.
Volume Serial Number is 7C07-CD3A
Directory of C:\Users\juliette\AppData\Roaming\Microsoft
01/15/2021 05:00 PM